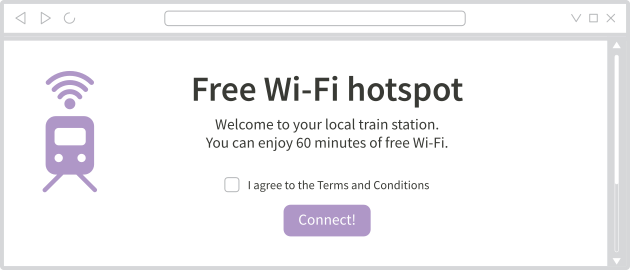
Qué son los portales cautivos
Un portal cautivo es una página web que a menudo se muestra antes de que puedas acceder a Internet en redes públicas de aeropuertos, hoteles, bibliotecas y otros lugares.
 .
.
Tails no puede conectarse a la red Tor cuando la conexión a Internet está inicialmente bloqueada por un portal cautivo.
The Unsafe Browser is not anonymous
El Navegador No Seguro no utiliza Tor. Los sitios web que visitas pueden ver tu dirección IP real.
Por eso te recomendamos que:
Only use the Unsafe Browser to sign in to a network using a captive portal or browse trusted web pages on the local network.
Close the Unsafe Browser after signing in to the network.
To learn how Tails implements the Unsafe Browser and its security, see our design documentation about the Unsafe Browser.
Starting the Unsafe Browser
Para iniciar el Navegador No seguro:
- Selecciona Aplicaciones ▸ Internet ▸ Navegador No Seguro.
Ingresar a la red usando un portal cautivo
Para iniciar sesión en una red usando un portal cautivo:
Try visiting an innocent-looking website that is common in your location, for example, a search engine or news site:
If you are redirected to a captive portal, sign in to the network.
If you are not redirected to a captive portal and the website loads, this means that you are already connected to the Internet. Close this browser the Unsafe Browser and try connecting to the Tor network again.
After Tails is connected to Tor, close this browser. the Unsafe Browser.
It is particularly important that you close the Unsafe Browser if you use accessibility features like the Screen Keyboard or the Screen Reader. If you keep the Unsafe Browser open, a very advanced network attacker might use it to deanonymize you.
You can use Tor Browser or any other application as usual.
